Since the day of its adoption, the European Union General Data Protection Regulation, or GDPR, has represented for organisations both a regulation to be in compliance with and a challenge. As a regulation, it has established and provided plain and straightforward requirements an organisation should apply when processing the personal data of employees, customers, and suppliers. As a challenge, the GDPR should be considered as the chance for a company, no matter if it’s small, medium, or big, to evaluate its organisational security processes. Can the GDPR enhance security in your company? Learn more in this article.
Does data protection mean security?
The GDPR is a regulation written and issued about protecting the rights of individuals over the use of their personal data. As a regulatory model, the GDPR especially deals with principles and rights every organisation is expected to follow in managing and protecting personal data. However, the GDPR avoids identifying the most appropriate tools a company should choose to implement this set of rules. This is because every company or organisation is different from the others and, for example, the same data processing, which could be a high risk for one company, could represent a low one for another that does business in a different field.
At the same time, the GDPR recommends an organisation to put in place security measures in order to ensure a proper level of security over any data processing, especially in cases of processing that is likely to result in a high risk to the rights and freedoms of natural persons. Just because a company’s data is compliant with the GDPR does not necessarily mean the data is secure. Data protection is only part of the security effort, implying the implementation of measures, policies, and procedures regarding security inside an organisation.
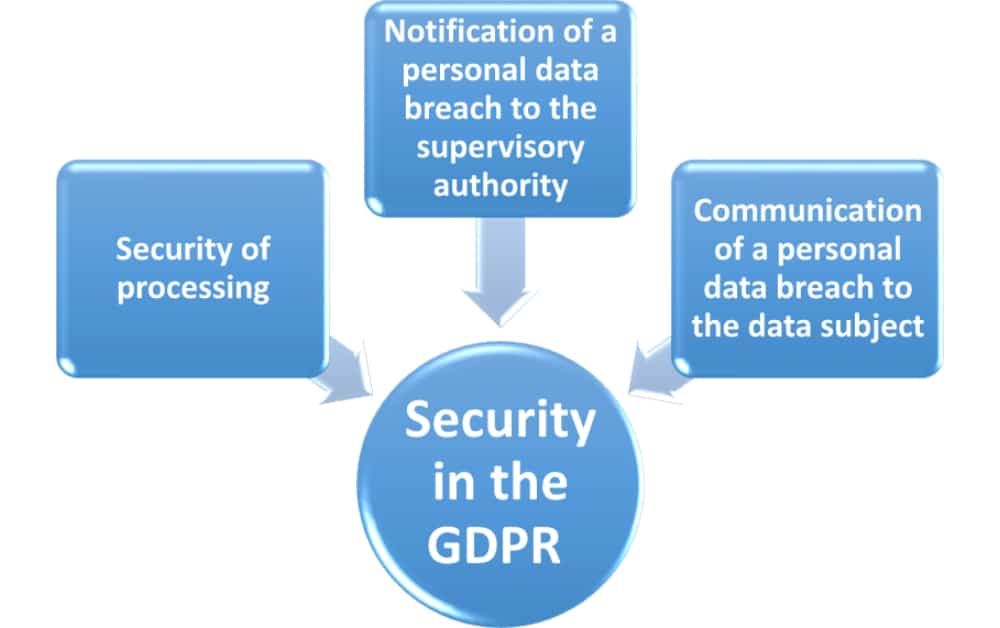
Security in the GDPR
Although the term “security” is not included in the list of definitions in article 4, the GDPR dedicates a full section to this topic, in section II, named “Security of personal data,” which includes articles 32, 33, and 34.
Article 32 is explicitly dedicated to underlining the importance of the security of processing. According to it, the controller and the processor will implement appropriate technical and organisational measures to ensure a level of security appropriate to the risk, taking into account the state of the art, the costs of implementation, and the nature, scope, context, and purposes of the processing. Some measures are listed as examples of appropriate ones, such as the pseudonymisation and the encryption of personal data.
Learn more about the roles of the controller and processor in the article EU GDPR controller vs. processor – What are the differences?
Article 33 and article 34 pertain to steps to be taken in case of a personal data breach. Article 33 states that the controller will, without undue delay and, where feasible, not later than 72 hours after having become aware of the breach, notify the supervisory authority, unless the personal data breach is unlikely to result in a risk to the rights and freedoms of natural persons.
Article 34 states that when the personal data breach is likely to result in a high risk to the rights and freedoms of natural persons, the controller will communicate the personal data breach to the data subject without undue delay. For more about data breaches, read the article 5 steps to handle a data breach according to GDPR.
The security functions and processes affected by the GDPR
Handling personal data means dealing with something that could be at a high risk. Personal data means any information that could identify, directly or indirectly, a natural person. This includes their name, address, date of birth, and ID numbers. Sometimes, data processing could include special categories of personal data, such as racial and ethnic data, health and genetic data, political opinions, religious or philosophical beliefs, or even sexual orientation.
In enlisting categories of data and the basic rights of any data subjects, the GDPR implicitly asks any controller and processor to determine in the clearest way:
- the data withheld by the company;
- all types of processing, including profiling or those for direct marketing purposes;
- if the information about the personal data being processed is provided to the data subject in a clear manner;
- if and how consent for data collection is obtained and managed;
- if any security measure is necessary, considering the type and the purposes of processing and, most of all, the nature and the impact of the risk that personal data could be exposed to in case of loss, damage, breach, or stealing of the same data.
Since the first days of its application, it’s undeniable that many companies have considered the GDPR as just an obligation to be compliant with. However, the GDPR is much more than this. It’s a code of conduct, a sort of guideline for every company to review its assets regarding the management of personal data. The regulation suggests that privacy could and should be a culture to practice, not only a set of requirements affecting the security functions in every organisation.
Consequently, an organisation is recommended to establish and implement a security framework for protecting and managing data. A security framework could be summarised as follows:
- a policy regarding personal data and basic data subjects’ rights written and communicated to every member of the company;
- a policy regarding possible transfers of personal data;
- an inventory of assets associated with personal information held and processed by the company (including the organisation’s assets accessible by suppliers);
- a set of procedures to implement in case of a security incident;
- a regular risk assessment regarding personal data to test and evaluate the effectiveness of the technical and organisational measures implemented to ensure the security of processing.
Learn more about the connection of ISO 27001 with the GDPR in the article Does ISO 27001 implementation satisfy EU GDPR requirements?
Privacy and security are two sides of the same coin
This framework is not willing to represent another requirement or rule that every organisation should abide by. Privacy is not a requirement. It represents a culture and a behaviour, something dealing with the daily working routine and with the security measures that can be implemented or improved in order to avoid or reduce the likelihood of data penetration. That is the reason why privacy involves security. They are two sides of the same coin.
To implement EU GDPR easily and efficiently, use our EU GDPR Premium Documentation Toolkit that provides step-by-step guidance and all documents for full EU GDPR compliance.

 Francesca Lucarini
Francesca Lucarini