If you’re starting to implement ISO 27001, you’re probably looking for a way to make your job easier, and the best approach would be automating repeatable activities and the creation of reports.
In this article, we’ll show you how the creation of the Statement of Applicability, one of the central documents of an ISMS compliant with ISO 27001, can be automated, based on information previously gathered during the start of the implementation, and how this is done on the Conformio platform.
What is the Statement of Applicability?
The Statement of Applicability (SoA) is the main link between the risk assessment & treatment and the implementation of your information security. This is a document that covers ISO 27001 clause 6.1.3 d, defining:
- which controls from ISO 27001 Annex A, as well as security measures from other sources (e.g., NIST, ENISA, SANS, etc.), will be applied
- justification for applicable controls, as well as for those found not applicable
- the implementation status of applicable controls
Additionally, as a good practice, you can include the manner in which the controls will be implemented (e.g., documentation of policies or procedures, description of activities to be performed, implementation of technologies, etc.), and objectives to be achieved (this latest addition to fulfill clause 6.2).
For more information about the Statement of Applicability, please read: The importance of Statement of Applicability for ISO 27001.
What is ISO 27001 Annex A?
Annex A of ISO 27001 is a set of suggested security controls to be used to improve the security of information.
It consists of 114 controls, organized into 14 domains, numbered A.5 through A.18, covering organizational controls, human resources, information technology, physical security, and legal issues.
The best way to understand Annex A is to think of it as a catalogue of information security controls you can select from – out of the 114 controls that are listed in Annex A, you can choose the ones that are applicable to your company’s needs.
For more information about Annex A controls, please read A quick guide to ISO 27001 controls from Annex A.
How do you write a Statement of Applicability?
To write a Statement of Applicability, you need:
- the list of controls from ISO 27001 Annex A, so you do not miss any control that needs to be in the SoA
- a list of legal, regulatory, contractual, and other requirements relevant to information security, identified at the beginning of the implementation, to provide justification for implementation of the required controls
- the results of risk treatment, to provide justification for the implementation of controls required to treat relevant risks
As justification for not applying a control from ISO 27001 Annex A, you can write that there are no relevant risks, or legal requirements, demanding the control’s implementation.
As you can see, when you work manually on the SoA you will need to gather several documents and make cross references to elaborate the SoA, and this can take a lot of time. But what if you could use an automated solution?
How to automate the SoA with Conformio
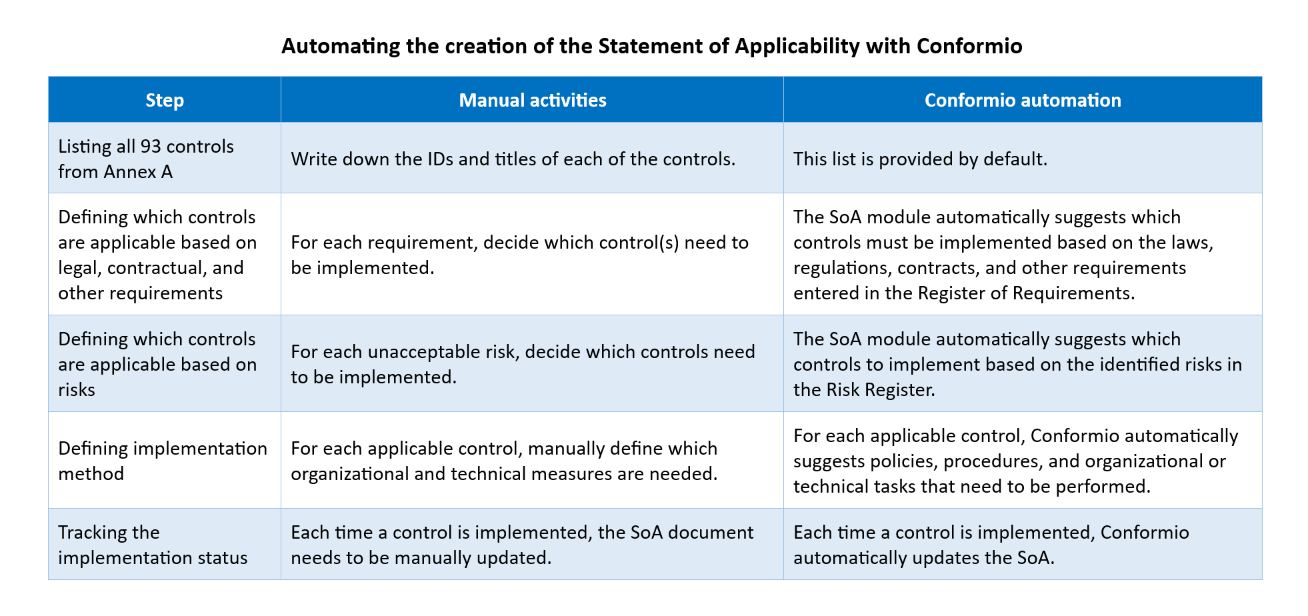
Conformio is an online platform for implementation and operation of an ISO 27001 Information Security Management System. It integrates its registers and modules data in a way that allows you to easily build documents based on already performed tasks, like the “Statement of Applicability” module (see the image below), which is integrated with the “Register of Requirements” and the “Risk Register.”
Let’s see how Conformio can help you automate the creation of the Statement of Applicability:
Automate what you can, and focus on managing what is important
Repetitive tasks, as well as setting up and creation of reports, are good candidates for automation. Besides the ISO 27001 Statement of Applicability showed in this article, activities like periodic reviews, dissemination of information, and presentation of performance indicators are other examples of what you can automate in your ISO 27001 implementation.
By automating such tasks, you minimize the need for human interaction, reducing administrative costs and risks of errors in data processing. Even better, you save time and effort to focus on analyzing information that can support decision making, the activities which really add value to the business when dealing with information security.
To automate your compliance with ISO 27001 security controls, sign up for a free trial of Conformio, the leading ISO 27001 compliance software.

 Rhand Leal
Rhand Leal