 Antonio Jose Segovia
Antonio Jose Segovia
October 26, 2015
Implementation, maintenance, training, and knowledge products for Information Security Management Systems (ISMS) according to the ISO 27001 standard.
Automate your ISMS implementation and maintenance with the Risk Register, Statement of Applicability, and wizards for all required documents.
All required policies, procedures, and forms to implement an ISMS according to ISO 27001.
Train your key people about ISO 27001 requirements and provide cybersecurity awareness training to all of your employees.
Accredited courses for individuals and security professionals who want the highest-quality training and certification.
Create ISO 27001 documentation, get instant answers to any questions related to ISO 27001 and the ISMS, refine your writing, and build security training materials faster with Advisera’s AI-powered platform.
Compliance and training products for critical infrastructure organizations for the European Union’s Network and Information Systems cybersecurity directive.
All required policies, procedures, and forms to comply with the NIS 2 cybersecurity directive.
Company-wide training program for employees and senior management to comply with Article 20 of the NIS 2 cybersecurity directive.
Create NIS2 documentation, refine your writing, and build security awareness training materials faster with Advisera’s AI-powered platform.
Compliance and training products for financial entities for the European Union’s DORA regulation.
All required policies, procedures, and forms to comply with the DORA regulation.
Company-wide cybersecurity and resilience training program for all employees, to train them and raise awareness about ICT risk management.
Accredited courses for individuals and DORA professionals who want the highest-quality training and certification.
Create DORA documentation, refine your writing, and build financial sector cybersecurity training materials faster with Advisera’s AI-powered platform.
Training products for Artificial Intelligence Management Systems (AIMS) and AI governance according to the ISO 42001 standard.
Accredited courses for individuals, consultants, and AI professionals who want the highest-quality training and certification in AI governance and compliance.
Train your key people on ISO 42001 requirements and provide company-wide AI governance training so employees learn how to use AI responsibly and in compliance with your policies.
Build structured training materials faster and refine your writing using Advisera’s AI-powered platform built on proprietary compliance knowledge.
Compliance and training products for personal data protection according to the European Union’s General Data Protection Regulation.
All required policies, procedures, and forms to comply with the EU GDPR privacy regulation.
Train your key people about GDPR requirements to ensure awareness of data protection principles, privacy rights, and regulatory compliance.
Accredited courses for individuals and privacy professionals who want the highest-quality training and certification.
Build structured training materials faster and refine your writing using Advisera’s AI-powered platform built on proprietary compliance knowledge.
Implementation, training, and knowledge products for Quality Management Systems (QMS) according to the ISO 9001 standard.
All required policies, procedures, and forms to implement a QMS according to ISO 9001.
Accredited courses for individuals and quality professionals who want the highest-quality training and certification.
Get instant answers to any questions related to ISO 9001 and the QMS, refine your writing, and build training materials faster with Advisera’s AI-powered platform built on proprietary compliance expertise.
Implementation, training, and knowledge products for Environmental Management Systems (EMS) according to the ISO 14001 standard.
All required policies, procedures, and forms to implement an EMS according to ISO 14001.
Accredited courses for individuals and environmental professionals who want the highest-quality training and certification.
Get instant answers to any questions related to ISO 14001 and the EMS, refine your writing, and build training materials faster with Advisera’s AI-powered platform built on proprietary compliance expertise.
Implementation and training products for Occupational Health & Safety Management Systems (OHSMS) according to the ISO 45001 standard.
All required policies, procedures, and forms to implement an OHSMS according to ISO 45001.
Accredited courses for individuals and health & safety professionals who want the highest-quality training and certification.
Build structured training materials faster and refine your writing using Advisera’s AI-powered platform built on proprietary compliance knowledge.
Implementation and training products for medical device Quality Management Systems (QMS) according to the ISO 13485 standard.
All required policies, procedures, and forms to implement a medical device QMS according to ISO 13485.
Accredited courses for individuals and medical device professionals who want the highest-quality training and certification.
Build structured training materials faster and refine your writing using Advisera’s AI-powered platform built on proprietary compliance knowledge.
Compliance products for the European Union’s Medical Device Regulation.
All required policies, procedures, and forms to comply with the EU MDR.
Build structured training materials faster and refine your writing using Advisera’s AI-powered platform built on proprietary compliance knowledge.
Implementation products for Information Technology Service Management Systems (ITSMS) according to the ISO 20000 standard.
All required policies, procedures, and forms to implement an ITSMS according to ISO 20000.
Build structured training materials faster and refine your writing using Advisera’s AI-powered platform built on proprietary compliance knowledge.
Implementation products for Business Continuity Management Systems (BCMS) according to the ISO 22301 standard.
All required policies, procedures, and forms to implement a BCMS according to ISO 22301.
Build structured training materials faster and refine your writing using Advisera’s AI-powered platform built on proprietary compliance knowledge.
Implementation products for testing and calibration laboratories according to the ISO 17025 standard.
All required policies, procedures, and forms to implement ISO 17025 in a laboratory.
Build structured training materials faster and refine your writing using Advisera’s AI-powered platform built on proprietary compliance knowledge.
Implementation products for automotive Quality Management Systems (QMS) according to the IATF 16949 standard.
All required policies, procedures, and forms to implement an automotive QMS according to IATF 16949.
Build structured training materials faster and refine your writing using Advisera’s AI-powered platform built on proprietary compliance knowledge.
Implementation products for aerospace Quality Management Systems (QMS) according to the AS9100 standard.
All required policies, procedures, and forms to implement an aerospace QMS according to AS9100.
Build structured training materials faster and refine your writing using Advisera’s AI-powered platform built on proprietary compliance knowledge.
Implementation, maintenance, training, and knowledge products for consultancies.
Handle multiple ISO 27001 projects by automating repetitive tasks during ISMS implementation.
All required policies, procedures, and forms to implement various standards and regulations for your clients.
Grow your business by organizing cybersecurity and compliance training for your clients under your own brand using Advisera’s learning management system platform.
Accredited Lead Auditor and Implementer courses for DORA and ISO standards, and advanced courses to help consultants grow their business, increase recurring revenue, and stand out from bigger competitors.
Create compliance documents, get instant answers to compliance questions, build training materials faster, and refine writing using Advisera’s AI-powered platform built on proprietary compliance knowledge.
Find new clients, potential partners, and collaborators and meet a community of like-minded professionals locally and globally.
Implementation, maintenance, training, and knowledge products for the IT industry.
Automate your ISMS implementation and maintenance with the Risk Register, Statement of Applicability, and wizards for all required documents.
Documentation to comply with ISO 27001 (cybersecurity), ISO 22301 (business continuity), ISO 20000 (IT service management), GDPR (privacy), NIS 2 (critical infrastructure cybersecurity), and DORA (cybersecurity for financial sector).
Company-wide cybersecurity awareness program for all employees, to decrease incidents and support a successful cybersecurity, privacy, and AI program.
Accredited courses for individuals and security professionals who want the highest-quality training and certification.
Create ISO 27001 and NIS2 documentation, get instant answers to any questions related to ISO 27001 and the ISMS, refine your writing, and build security training materials faster with Advisera’s AI-powered platform
Compliance, training, and knowledge products for essential and important organizations.
Documentation to comply with NIS 2 (cybersecurity), GDPR (privacy), ISO 27001 (cybersecurity), and ISO 22301 (business continuity).
Company-wide training program for employees and senior management to comply with Article 20 of the NIS 2 cybersecurity directive.
Accredited courses for individuals and security professionals who want the highest-quality training and certification.
Create ISO 27001 and NIS2 documentation, get instant answers to any questions related to ISO 27001 (ISMS), refine your writing, and build security awareness training materials faster with Advisera’s AI-powered platform
Implementation, training, and knowledge products for manufacturing companies.
Documentation to comply with ISO 9001 (quality), ISO 14001 (environmental), and ISO 45001 (health & safety), and NIS 2 (critical infrastructure cybersecurity).
Company-wide cybersecurity awareness program for all employees, to decrease incidents and support a successful cybersecurity program.
Accredited courses for individuals and professionals who want the highest-quality training and certification.
Get instant answers to any questions related to ISO 9001 (QMS) and ISO 14001 (EMS), refine your writing, and build training materials faster with Advisera’s AI-powered platform built on proprietary compliance expertise.
Implementation, training, and knowledge products for transportation & distribution companies.
Documentation to comply with ISO 9001 (quality), ISO 14001 (environmental), and ISO 45001 (health & safety), and NIS 2 (critical infrastructure cybersecurity).
Company-wide cybersecurity awareness program for all employees, to decrease incidents and support a successful cybersecurity program.
Accredited courses for individuals and professionals who want the highest-quality training and certification.
Get instant answers to any questions related to ISO 9001 (QMS) and ISO 14001 (EMS), refine your writing, and build training materials faster with Advisera’s AI-powered platform built on proprietary compliance expertise.
Implementation, training, and knowledge products for schools, universities, and other educational organizations.
Documentation to comply with ISO 27001 (cybersecurity), ISO 9001 (quality), and GDPR (privacy).
Company-wide cybersecurity and AI governance awareness program for all employees, to decrease incidents, support a successful cybersecurity program, and ensure responsible use of AI.
Accredited courses for individuals and professionals who want the highest-quality training and certification.
Get instant answers to any questions related to ISO 9001 (QMS) and ISO 14001 (EMS), refine your writing, and build training materials faster with Advisera’s AI-powered platform built on proprietary compliance expertise.
Implementation, maintenance, training, and knowledge products for telecoms.
Automate your ISMS implementation and maintenance with the Risk Register, Statement of Applicability, and wizards for all required documents.
Documentation to comply with ISO 27001 (cybersecurity), ISO 22301 (business continuity), ISO 20000 (IT service management), GDPR (privacy), and NIS 2 (critical infrastructure cybersecurity).
Company-wide cybersecurity awareness program for all employees, to decrease incidents and support a successful cybersecurity program.
Accredited courses for individuals and security professionals who want the highest-quality training and certification.
Create ISO 27001 and NIS2 documentation, get instant answers to any questions related to ISO 27001 (ISMS), refine your writing, and build security awareness training materials faster with Advisera’s AI-powered platform.
Implementation, maintenance, training, and knowledge products for banks, insurance companies, and other financial organizations.
Automate your ISMS implementation and maintenance with the Risk Register, Statement of Applicability, and wizards for all required documents.
Documentation to comply with DORA (cybersecurity for financial sector), ISO 27001 (cybersecurity), ISO 22301 (business continuity), and GDPR (privacy).
Company-wide cybersecurity awareness program for all employees, to decrease incidents and support a successful cybersecurity, privacy, and AI program.
Accredited courses for individuals and security professionals who want the highest-quality training and certification.
Create ISO 27001 and NIS2 documentation, get instant answers to any questions related to ISO 27001 (ISMS), refine your writing, and build security awareness training materials faster with Advisera’s AI-powered platform.
Implementation, training, and knowledge products for local, regional, and national government entities.
Documentation to comply with ISO 27001 (cybersecurity), ISO 9001 (quality), GDPR (privacy), and NIS 2 (critical infrastructure cybersecurity).
Company-wide cybersecurity awareness program for all employees, to decrease incidents and support a successful cybersecurity, privacy, and AI program.
Accredited courses for individuals and professionals who want the highest-quality training and certification.
Get instant answers to any questions related to ISO 27001 (ISMS) and ISO 9001 (QMS), refine your writing, and build training materials faster with Advisera’s AI-powered platform built on proprietary compliance expertise.
Implementation, training, and knowledge products for hospitals and other health organizations.
Documentation to comply with ISO 27001 (cybersecurity), ISO 9001 (quality), ISO 14001 (environmental), ISO 45001 (health & safety), NIS 2 (critical infrastructure cybersecurity) and GDPR (privacy).
Company-wide cybersecurity and AI governance awareness program for all employees, to decrease incidents, support a successful cybersecurity program, and ensure responsible use of AI.
Accredited courses for individuals and professionals who want the highest-quality training and certification.
Get instant answers to any questions related to ISO 27001 (ISMS), ISO 9001 (QMS), and ISO 14001 (EMS), refine your writing, and build training materials faster with Advisera’s AI-powered platform built on proprietary compliance expertise.
Implementation, training, and knowledge products for the medical device industry.
Documentation to comply with ISO 13485 (medical device), ISO 27001 (cybersecurity), ISO 9001 (quality), ISO 14001 (environmental), ISO 45001 (health & safety), NIS 2 (critical infrastructure cybersecurity) and GDPR (privacy).
Company-wide cybersecurity awareness program for all employees, to decrease incidents and support a successful cybersecurity, privacy, and AI program.
Accredited courses for individuals and professionals who want the highest-quality training and certification.
Get instant answers to any questions related to ISO 27001 (ISMS), ISO 9001 (QMS), and ISO 14001 (EMS), refine your writing, and build training materials faster with Advisera’s AI-powered platform built on proprietary compliance expertise.
Implementation, training, and knowledge products for the aerospace industry.
Documentation to comply with AS9100 (aerospace), ISO 9001 (quality), ISO 14001 (environmental), and ISO 45001 (health & safety), and NIS 2 (critical infrastructure cybersecurity).
Company-wide cybersecurity awareness program for all employees, to decrease incidents and support a successful cybersecurity program.
Accredited courses for individuals and professionals who want the highest-quality training and certification.
Get instant answers to any questions related to ISO 9001 (QMS) and ISO 14001 (EMS), refine your writing, and build training materials faster with Advisera’s AI-powered platform built on proprietary compliance expertise.
Implementation, training, and knowledge products for the automotive industry.
Documentation to comply with IATF 16949 (automotive), ISO 9001 (quality), ISO 14001 (environmental), and ISO 45001 (health & safety), and NIS 2 (critical infrastructure cybersecurity).
Company-wide cybersecurity awareness program for all employees, to decrease incidents and support a successful cybersecurity and AI program.
Accredited courses for individuals and professionals who want the highest-quality training and certification.
Get instant answers to any questions related to ISO 9001 (QMS) and ISO 14001 (EMS), refine your writing, and build training materials faster with Advisera’s AI-powered platform built on proprietary compliance expertise.
Implementation, training, and knowledge products for laboratories.
Documentation to comply with ISO 17025 (testing and calibration laboratories), ISO 9001 (quality), and NIS 2 (critical infrastructure cybersecurity).
Company-wide cybersecurity awareness program for all employees, to decrease incidents and support a successful cybersecurity program.
Accredited courses for individuals and quality professionals who want the highest-quality training and certification.
Get instant answers to any questions related to ISO 9001 (QMS), refine your writing, and build training materials faster with Advisera’s AI-powered platform built on proprietary compliance expertise.
 Antonio Jose Segovia
Antonio Jose Segovia
Updated: January 20, 2025, according to the ISO 27001:2022 revision.
One of the issues that most concern managers of an organization is that their employees (although employees are not the only source of incidents, but also clients, providers, etc.) be able to work without any incident. However, this is practically impossible, because the people are not perfect, and therefore neither are information systems and technologies.
Thus, we can assume that incidents will happen in any organization, so it is necessary to establish a mechanism that will allow us to be ready when one occurs, or when someone – an employee, a contractor, third-party users of the systems – detects a weakness in the systems or services. The first step to achieve this is to establish a procedure to manage security incidents.
Before I continue with the article, let me remind you that ISO 27000 establishes the definition of a security incident in the following way: “a single or a series of unwanted or unexpected information security events that have a significant probability of compromising business operations and threatening information security.”
Now we are going to see in the following paragraphs the main things that you need to manage security incidents in accordance with the following ISO 27001 Annex A controls related to incident management:
The management of security incidents is based on different steps, which include:
Therefore, we can see that these could be different states that an incident could have, and it is also important to inform the user about any changes in the state of the incident.
Usually, we will define the following responsibilities:
If the company is small, the technicians for level 1 and level 2 can be the same person.
There are many ways of classifying incidents, but the usual is to consider two parameters:
The intersection of these parameters will allow us to determine the priority of each incident, so in this way you can set, for example, the following table of values:
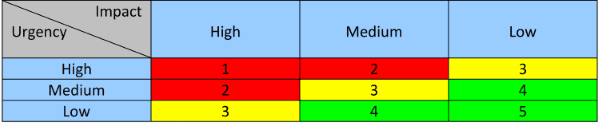
So, incidents with value 1 are critical because the urgency and impact are high, so they need to be resolved before the other incidents with values 2, 3, 4, or 5 (this is the right sequence to resolve incidents).
There are many tools on the market to manage security incidents. Most of them register any type of incident, but in this case it would be appropriate to ensure that these tools allow us to differentiate a security incident from other types of incidents.
However, it is not mandatory for an organization to use a specific software tool for managing security incidents. It is equally valid to use an Excel or Word template, to register all security incidents, and to control the status of each one. A software tool can be useful, but if the incidents are few, from my point of view, Excel may be a good option.
Finally, we cannot prevent all security incidents from occurring, because it is impossible, but we can treat them, which means that the organization can be prepared for security incidents and decrease the damage.
To implement policies and procedures for ISO 27001 Annex A controls, sign up for a free trial of Conformio, the leading ISO 27001 compliance software.


You may unsubscribe at any time. For more information, please see our privacy notice.
