Very often, I hear controversial discussions about whether information security is part of IT, or whether it should be separate from it, part of some compliance or risk department, etc.
But, before we determine who should be handling information security and from which organizational unit, let’s see first the conceptual point of view – where does information security fit into an organization?
Generally, information security is part of overall risk management in a company, with areas that overlap with cybersecurity, business continuity management, and IT management, as displayed below.
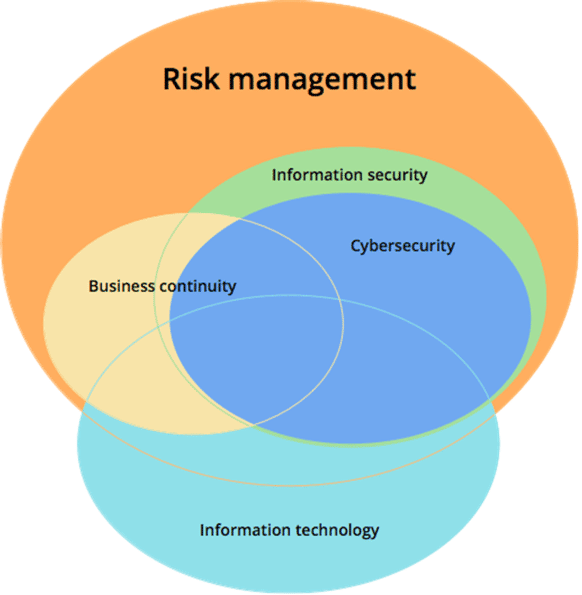
Figure: Relationship between information security, risk management, business continuity, IT, and cybersecurity
Cybersecurity is basically a subset of information security because it focuses on protecting the information in digital form, while information security is a slightly wider concept because it protects the information in any media.
The overlap with business continuity exists because its purpose is, among other things, to enable the availability of information, which is also one of the key roles of information security. See also this article: How to use ISO 22301 for the implementation of business continuity in ISO 27001.
Naturally, information technology plays an extremely important role in information security; so, consequently, there is also an overlapping area; information technology is not only about security, so this is why good part of IT is not related to security.
Why risk management?
But, the most important thing is that information security, cybersecurity, and business continuity have the same goal: to decrease the risks to business operations. You may not call it risk management in your day-to-day job, but basically this is what information security does – assess which potential problems can occur, and then apply various safeguards or controls to decrease those risks.
Some industries have formally recognized information security as part of risk management – e.g., in the banking world, information security belongs very often to operational risk management. My guess is that in the future we will see more and more information security professionals work in the risk management part of their organizations, and information security will tend to merge with business continuity.
See also this article: Chief Information Security Officer (CISO) – where does he belong in an org chart?
Security is more than IT
So, the point is: thinking about information security only in IT terms is wrong – this is a way to narrow the security only to technology issues, which won’t resolve the main source of incidents: people’s behavior.
If you want your information security to be effective, you must enable it to access both IT and business parts of the organization – and for this to succeed, you will need at least two things: to change the perception about security, and to provide a proper organizational position for people handling security.
To automate your compliance with ISO 27001 security controls, sign up for a free trial of Conformio, the leading ISO 27001 compliance software.

 Dejan Kosutic
Dejan Kosutic 


