If you are asking what ISO 27001, PCI-DSS, and information security are, then now is the time to learn. First of all, I recommend that you read this article: What is ISO 27001?. Basically, there are many standards in information security, but two that have special relevance for their scope and for their international impact are ISO 27001 and PCI-DSS. In this article, we will see a general description and structure of each one.
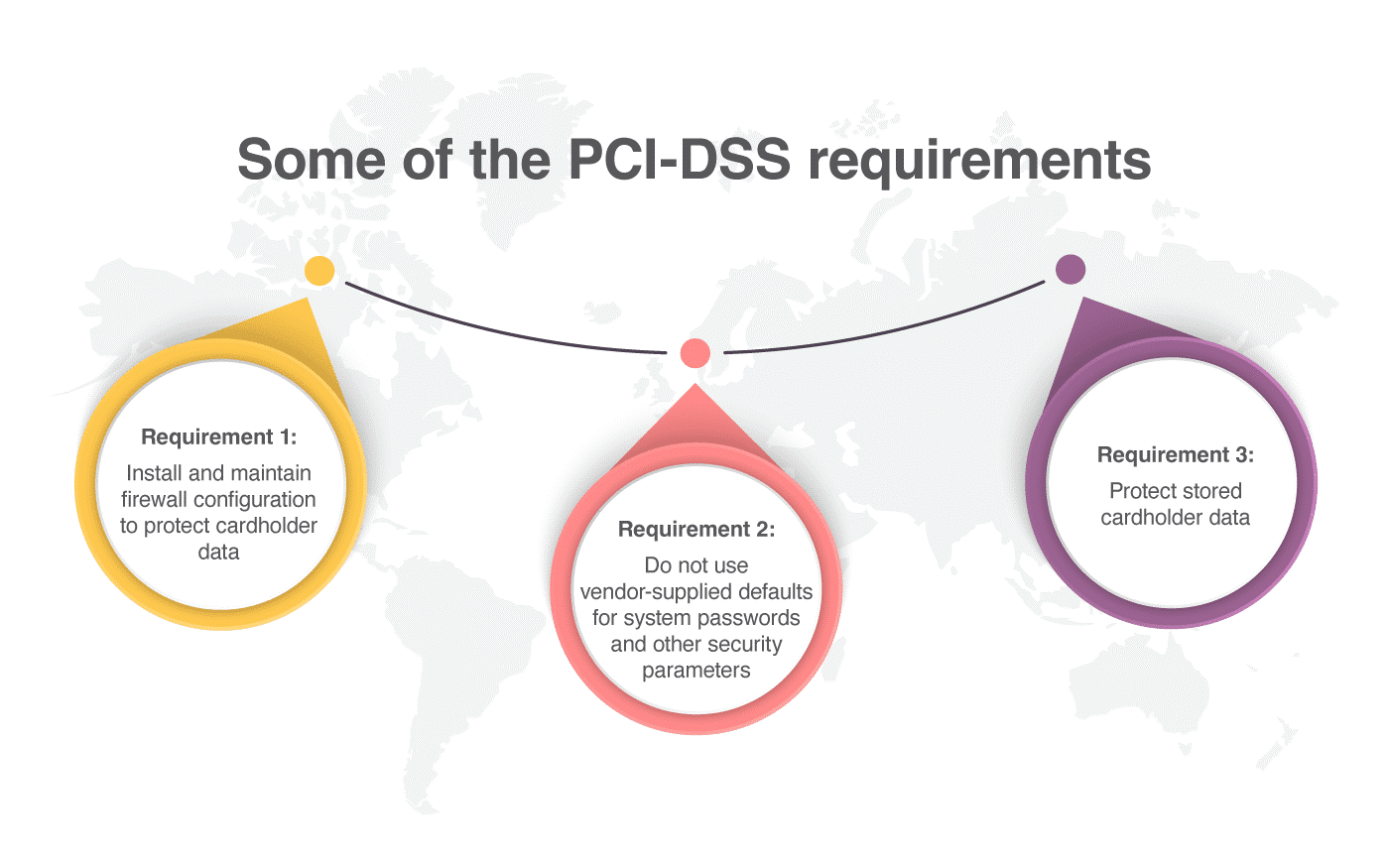
PCI-DSS is a standard of data security for the credit card industry, and applies only to companies that process, store, or transmit credit card data. For these companies, compliance with the standard is obligatory, though depending on the volume of cards processed, different requirements or obligations may apply. Some of the PCI-DSS requirements are:
- Requirement 1: Install and maintain firewall configuration to protect cardholder data.
- Requirement 2: Do not use vendor-supplied defaults for system passwords and other security parameters.
- Requirement 3: Protect stored cardholder data.
What is ISO 27001 and what is PCI-DSS?
It is possible that many organizations have this question in mind, and the answer will obviously depend on the needs of each business. Anyway, let’s see them:
- ISO 27001 is an international standard, with worldwide recognition, that lays down the requirements for the establishment of an Information Security Management System. It applies to any type of organization, and their implementation and certification is optional, so it is not mandatory for a company.
- PCI-DSS is a standard of data security for the credit card industry, and applies only to companies that process, store, or transmit credit card data. For these companies, compliance with the standard is obligatory, though depending on the volume of cards processed, different requirements or obligations may apply.
One of the more important things that ISO 27001 has, and PCI-DSS does not have, is the PDCA (Plan, Do, Check, Act), which is established in any management system based on ISO. Therefore, keep in mind that ISO 27001 is better for those organizations where there is already a management system, and that want to supplement it with the security of the information (or do not have a management system and want it to protect the information), while PCI-DSS is most suitable, and mandatory, for those organizations that work with credit cards.
Structure of PCI-DSS
PCI-DSS consists of 13 groups of controls (12 requirements + 1 annex), and more than 200 controls that are focused on the security of the data of credit cards:
- Requirement 1: Install and maintain firewall configuration to protect cardholder data.
- Requirement 2: Do not use vendor-supplied defaults for system passwords and other security parameters.
- Requirement 3: Protect stored cardholder data.
- Requirement 4: Encrypt transmission of cardholder data across open, public networks.
- Requirement 5: Protect all systems against malware and regularly update anti-virus software or programs.
- Requirement 6: Develop and maintain secure systems and applications.
- Requirement 7: Restrict access to cardholder data by business need to know.
- Requirement 8: Identify and authenticate access to system components.
- Requirement 9: Restrict physical access to cardholder data.
- Requirement 10: Track and monitor all access to network resources and cardholder data.
- Requirement 11: Regularly test security systems and processes.
- Requirement 12: Maintain a policy that addresses information security for all personnel.
- Requirement A.1: Shared hosting providers must protect the cardholder data environment.
The content of this standard consists of 112 pages, is freely available, and can be consulted / downloaded from the official website of the PCI Security Standard Council. The document indicates the requirements and provides a guide to comply with them.
Similarities and differences between ISO 27001 and PCI-DSS
On the other hand, ISO 27001 consists of 11 clauses (starting at 0 and ending at 10) that are related to the management system, and it also has 13 groups of controls and 114 generic security controls that can be applied to any type of organization. Read this article to get an overview of the security controls: An overview of ISO 27001:2013 Annex A. Many of these controls have similarities with PCI-DSS:
- A.5 Information Security policies (is related to requirement 12 of PCI-DSS)
- A.6 Organization of information security (is related to requirement 12 of PCI-DSS)
- A.7 Human resource security (is related to requirement 12 of PCI-DSS)
- A.8 Asset management (is related to requirement 12 of PCI-DSS)
- A.9 Access control (is related to requirement 7 of PCI-DSS)
- A.10 Cryptography (is related to requirement 4 of PCI-DSS)
- A.11 Physical and environmental security (is related to requirement 9 of PCI-DSS)
- A.12 Operations security (is related to requirements 1, 5, 10, and 11 of PCI-DSS)
- A.13 Communications security (is related to requirement 4 of PCI-DSS)
- A.14 System acquisition, development and maintenance (is related to requirement 6 of PCI-DSS)
- A.15 Supplier relationships
- A.16 Information security incident management
- A.17 Information security aspects of business continuity management
- A.18 Compliance
The content of this standard consists of 30 pages, and is available from the main page of the ISO website, but you need to pay for it. The document only indicates the requirements, but if you want to know how you can comply with them, another standard is necessary: ISO 27002, which is a code of best practices.
How to use them?
So, as you can see, there are many similarities between both standards, for example the continuous improvement of ISO 27001, i.e., the best general security controls of ISO 27002, and the best security controls regarding credit cards in PCI-DSS. There are many companies that work with both standards and use the advantages of both of them to provide services to their customers with the best security. So, having in mind that they complement each other very well, and that for an acceptable effort you gain a lot, maybe it’s a good idea to consider implementation of both of them.
Implementation
Implementing and integrating both standards can be a great point of differentiation, because on the one hand we have a management system, and on the other hand we have generic security controls, and we can also have specific controls for credit card environments. In addition, since many controls of both standards are similar, the integration will be simple.
Therefore, if you work with credit card data and also want to have a management system to plan, implement, review, and improve security controls, then it can be a good opportunity for your organization to work with PCI-DSS and ISO 27001 together.
Certification schemes
One important thing after the implementation of these standards is the certification of them. The certification schemes of the two standards are completely different. ISO 27001 depends on the International Organization for Standardization (ISO), which is composed of members from all over the world, and it is audited by certification bodies that have to be accredited by national accreditation bodies. On the other hand, the auditor must be qualified by each certification body.
In the case of PCI-DSS, there is the central forum PCI Security Standards Council (PCI-SSC), which comprises the five most important payment process entities: Visa, MasterCard, American Express, Discover Financial Services, and JCB International. But, in this case, PCI-SSC does not manage compliance with the PCI-DSS standard; this must be done by each brand directly. This means that there is an external Qualified Security Assessor (QSA) that creates a Report on Compliance (ROC) for organizations handling large volumes of transactions, or a Self-Assessment Questionnaire (SAQ) for companies handling smaller values. And, it’s important to note here: To be a QSA you must work with a company approved by PCI-SSC.
What comes first?
If there is nothing implemented in your organization, it is better to start with the management system of ISO 27001, because with this you can manage both standards with an integrated system in a single way. So, in this case:
- Define the scope of the ISO 27001 ISMS.
- Implement the PDCA cycle and the risk assessment (the risk assessment is a common requisite between ISO 27001 and PCI-DSS).
- Implement the risk treatment (with the generic security controls).
- Implement the security controls related to credit cards.
Remember the structure of the controls of Annex A of ISO 27001 and the structure of PCI-DSS, which I discussed in the article linked at the beginning of this article.
Here it is also important to integrate the scope of both standards, so it is recommended that when you define the scope of ISO 27001, you keep in mind all systems and processes related to the credit card environment.
In addition, I think that if your organization has another ISO management system (for example, ISO 9001), you could also use the PDCA cycle for the management of the security controls of PCI-DSS.
Since PCI-DSS and ISO 27001 have similar security controls, you can integrate them in your company with the foundation of the PDCA cycle, which will give your organization a continuous improvement model, and also help your organization to manage generic security controls, including specific security controls for credit cards.
To learn how to become compliant with ISO 27001, sign up for a 14-day free trial of Conformio, the leading ISO 27001 compliance software.

 Antonio Jose Segovia
Antonio Jose Segovia