It may sound rather funny, but ISO 27001 does not require a company to nominate a Chief Information Security Officer, or any other person who would coordinate information security (e.g., Information security officer, Security manager, etc.).
However, this is understandable – ISO 27001 is written in such a way that it is applicable to companies of any size, in any industry, so requiring small companies to have a designated CISO would be overkill.
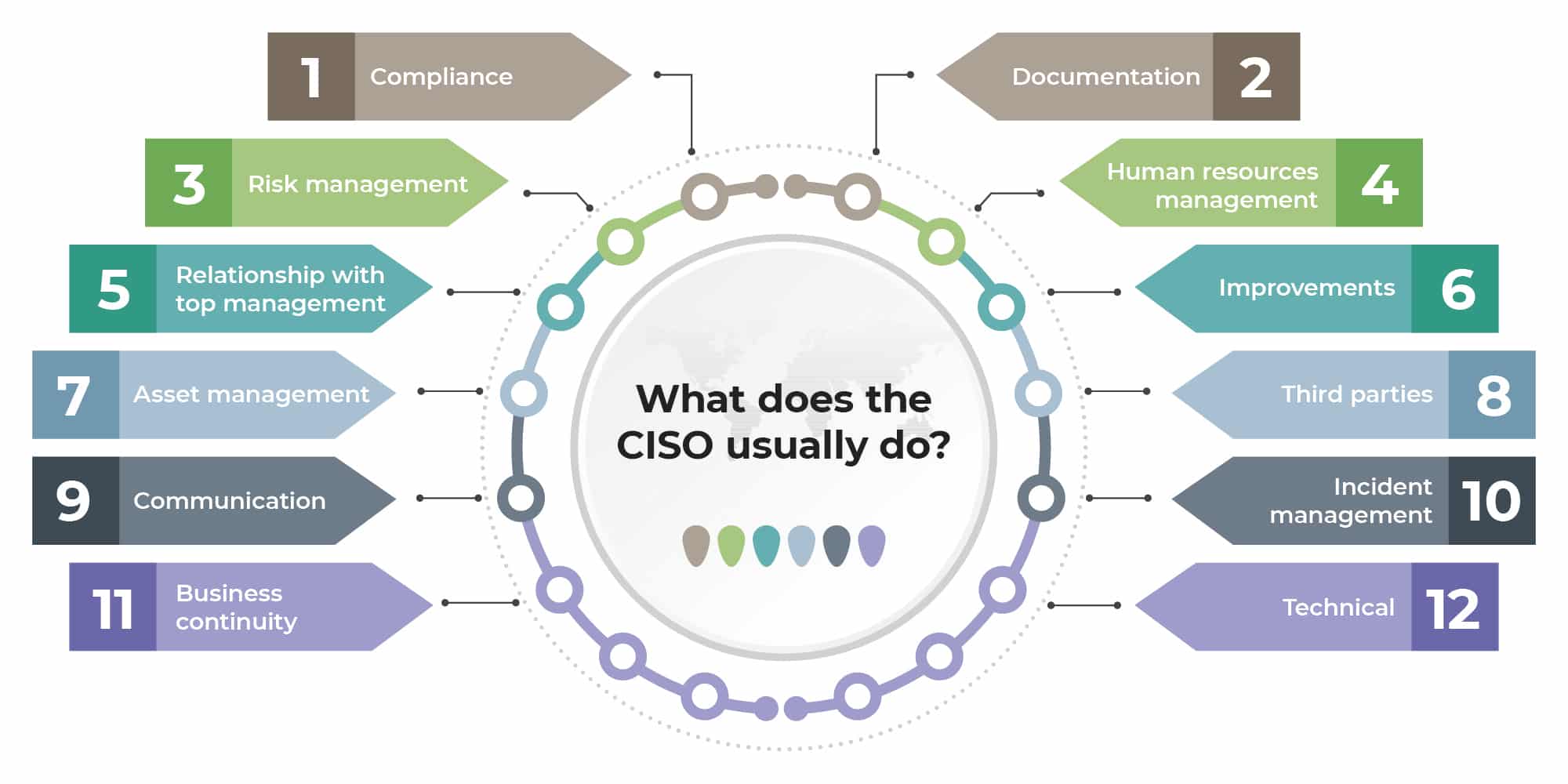
- Compliance
- Documentation
- Risk management
- Human resources management
- Relationship with top management
- Improvements
- Asset management
- Third parties
- Communication
- Incident management
- Business continuity
- Technical
What does the CISO usually do?
Since ISO 27001 does not require the CISO, it does not prescribe what this person should do, either – so it is up to you to decide what suits your company the best. Generally, this person should coordinate all the activities related to securing the information in a company, and here are some ideas on what this person could do (divided by ISO 27001 sections):
Compliance:
- Develop the list of interested parties related to information security (see also Who are interested parties, and how can you identify them according to ISO 27001 and ISO 22301?)
- Develop the list of requirements from interested parties
- Remain in continuous contact with authorities and special interest groups
- Coordinate all efforts related to personal data protection
Documentation:
- Propose the draft of main information security documents – e.g., Information security policy, Classification policy, Access control policy, Acceptable use of assets, Risk assessment and risk treatment methodology, Statement of Applicability, Risk treatment plan, etc.
- Be responsible for reviewing and updating main documents
Risk management:
- Teach employees how to perform risk assessment
- Coordinate the whole process of risk assessment (see also: ISO 27001 risk assessment & treatment – 6 main steps)
- Propose the selection of safeguards
- Propose the deadlines for safeguards implementation
Human resources management:
- Perform background verification checks of job candidates
- Prepare the training and awareness plan for information security (see also How to perform training & awareness for ISO 27001 and ISO 22301)
- Perform continuous activities related to awareness raising
- Performing induction training on security topics for new employees
- Propose disciplinary actions against employees who performed the security breach
Relationship with top management:
- Communicate the benefits of information security (see also Four key benefits of ISO 27001 implementation)
- Propose information security objectives (see also ISO 27001 control objectives – Why are they important?)
- Report on the results of measuring
- Propose security improvements and corrective actions
- Propose budget and other required resources for protecting the information
- Report important requirements of interested parties
- Notify top management about the main risks
- Report about the implementation of safeguards
- Advise top executives on all security matters
Improvements:
- Ensure that all corrective actions are performed
- Verify if the corrective actions have eliminated the cause of nonconformities
Asset management:
- Maintain an inventory of all important information assets
- Delete the records that are not needed any more
- Dispose of media and equipment no longer in use, in a secure way
Third parties:
- Perform risk assessment for activities to be outsourced
- Perform background check for candidates for outsourcing partners
- Define security clauses that must be part of an agreement
Communication:
- Define which type of communication channels are acceptable and which are not
- Prepare communication equipment to be used in case of an emergency / disaster
Incident management:
- Receive information about security incidents
- Coordinate response to security incidents
- Prepare evidence for legal action following an incident
- Analyze incidents in order to prevent their recurrence
Business continuity:
- Coordinate the business impact analysis process and the creation of response plans
- Coordinate exercising and testing
- Perform post-incident review of the recovery plans
Technical:
- Approve appropriate methods for the protection of mobile devices, computer networks and other communication channels
- Propose authentication methods, password policy, encryption methods, etc.
- Propose rules for secure teleworking
- Define required security features of Internet services
- Define principles for secure development of information systems
- Review logs of user activities in order to recognize suspicious behavior
How to document CISO responsibilities
As you can see, CISO responsibilities are quite numerous, and this person is involved in several very different areas of your company.
The larger the company, the more difficult it becomes to remember all these responsibilities, so depending on the size of your organization, you should produce one or several documents where you describe those. Some companies tend to list all the responsibilities of the CISO in a single document, which I personally don’t find very useful – this is because it is difficult to understand someone’s role without seeing the process it is part of.
Therefore, I think it is better to describe those responsibilities in several documents that detail those processes – for example, the CISO responsibilities related to human resources management should be described in the Human resource policy, responsibilities related to incidents in the Incident management procedure, etc.
Who should be the CISO?
In smaller companies, the role of CISO should be performed by someone along with his/her other duties – e.g., if you are a company of 10 employees, this could be done by your IT system administrator; if you have 100 employees this could be your IT manager. However, if your company has a couple of thousand employees, you should have at least one full-time person dedicated to this job, because it will consume this person full-time. See also: Chief Information Security Officer (CISO) – where does he belong in an org chart?
When selecting a person to be the CISO, your main criteria should not only be how knowledgeable this person is about information technology – I would say it is even more important that this person knows the business processes in your company, and has good interpersonal skills.
Why is this? Because the main job of the Chief Information Security Officer should be developing a risk-based security culture in a company. Just as one of the underlying principles in all companies is that all the activities are to be made profitable, the CISO should develop a similarly embedded mindset with security: that all the business activities create a certain level of security risk, and that such risk must be mitigated with safeguards – so that business would gain benefits.
To learn how to implement ISO 27001 through a step-by-step wizard and get all the necessary policies and procedures, sign up for a free trial of Conformio, the leading ISO 27001 compliance software.

 Dejan Kosutic
Dejan Kosutic