Updated: November 14, 2022., according to ISO 27001:2022 revision.
Classification of information is certainly one of the most attractive parts of information security management, but at the same time, one of the most misunderstood. This is probably due to the fact that historically, information classification was the first element of information security that was being managed — long before the first computer was built, governments, military, and even corporations labeled their information as confidential. However, the process of how it worked remained somewhat of a mystery.
So, in this article I’ll give you an outline of how information classification works, and how to make it compliant with ISO 27001, the leading information security standard. Although classification can be done according to other criteria, I’m going to speak about classification in terms of confidentiality, because this is the most common way to specify information classification levels.
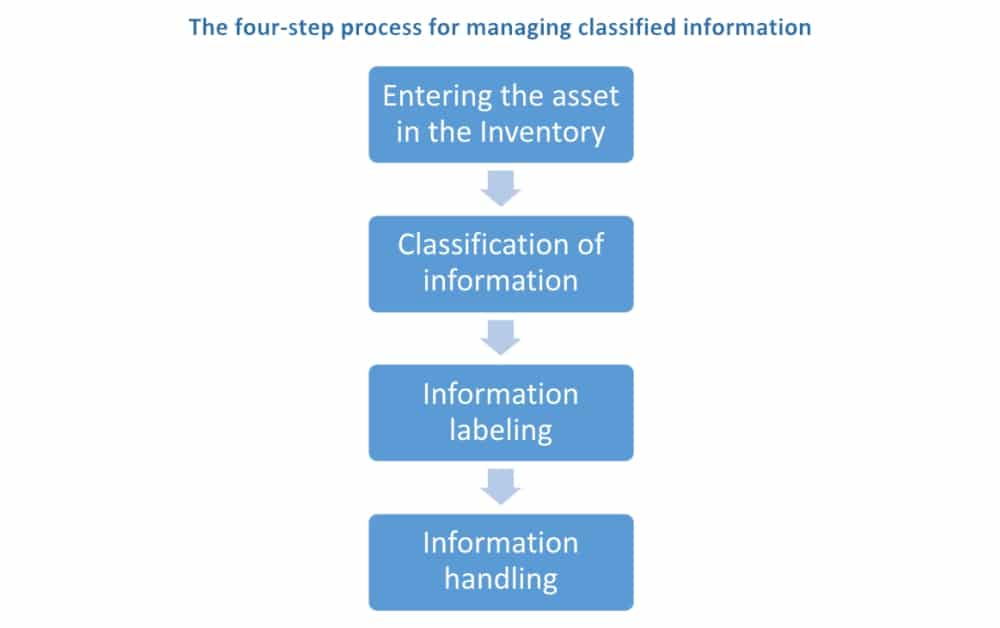
- Entering the asset in the Inventory of Assets
- Classification of information
- Information labelling
- Information handling
The four-step process for classifying information
Good practice for classifying information says that classification should be done via the following process:
This means that: (1) the information should be entered in the Inventory of Assets (control A.5.9 of ISO 27001), (2) it should be classified (A.5.12), (3) it should be labeled (A.5.13), and finally, (4) it should be handled in a secure way (A.5.10).
In most cases, companies will develop an Information Classification Policy, which should describe all these four steps for classifying information — see the text below for each of these steps.
Please note that this process applies to both data (the raw recorded material that has no specific meaning) and information (the meaning you give to, and insights you get from data). In a classification context, generally data and information are treated the same.
Entering the asset in the inventory (asset register)
The point of entering the asset in the inventory is that you know which information you have in your possession, and who is responsible for it (i.e., who is the owner).
Information can be in different forms and types of media, e.g.:
- electronic documents
- information systems / databases
- paper documents
- storage media (e.g., disks, memory cards, etc.)
- information transmitted verbally
Classification of information
The purpose of classifying information is to categorize it based on its level of sensitivity and its importance to the organization. Normally, the higher the classification level, the more important the information is.
This helps organizations to understand the importance of each type of information for them, and to prioritize information protection efforts (information with higher classification levels would require more resources for its protection), increasing information security and regulatory compliance.
The most common attribute used for information classification is confidentiality, although you can also find classifications based on integrity and availability.
Who is responsible for classifying information?
In most cases, the asset owner is responsible for the confidentiality classification of the information, and this is usually done based on the results of the risk assessment: The higher the value of the information (i.e., the higher the consequence of breaching confidentiality), the higher the classification level should be. (See also ISO 27001 Risk Assessment, Treatment, & Management: The Complete Guide.)
Defining confidentiality levels
ISO 27001 does not prescribe document classification levels or information classification levels (i.e., there are no ISO 27001 information classification or ISO 27001 data classification schemes, or other classification standards) — this is something you should develop on your own, based on what is common in your country or in your industry.
Examples of information classification levels
The bigger and more complex your organization is, the more levels of confidentiality you will have — for example, for a mid-size organization you may use these kinds of information classification levels with three confidential levels and one public level:
- Confidential (top confidentiality level)
- Restricted (medium confidentiality level)
- Internal use (lowest level of confidentiality)
- Public (everyone can see the information)
Very often, a company may have two different classification schemes in place if it works both with the government and in the private sector. For example, NATO requires the following classification with four confidential levels and two public levels:
- Cosmic Top Secret
- NATO Secret
- NATO Confidential
- NATO Restricted
- NATO Unclassified (copyright)
- NON SENSITIVE INFORMATION RELEASABLE TO THE PUBLIC
However, is important to note that in very specific situations, where information importance is homogeneous, organizations can adopt a single classification level. It is perfectly acceptable by the standard to use single or multiple confidentiality levels as the ISO 27001 information classification/ISO 27001 data classification structure.
Information labeling
Once you classify the information, then you need to label it appropriately — you should develop the guidelines for each type of information asset on how it needs to be classified — again, ISO 27001 is not prescriptive here, so you can develop your own rules.
For example, you could set the rules for paper documents such that the confidentiality level is to be indicated in the top right corner of each document page, and that it is also to be indicated on the front of the cover or envelope carrying such a document, as well as on the filing folder in which the document is stored.
Labeling of information is usually the responsibility of the asset owner.
Information handling
This is usually the most complex part of the classification process — you should develop rules on how to protect each type of asset depending on the level of confidentiality. For example, you could use a table in which you must define the rules for each level of confidentiality for each type of media, e.g.:
| Internal use | Restricted | Confidential | |
| Electronic documents | |||
| Information systems | |||
| Paper documents | |||
| Storage media | |||
| Verbally transmitted information | |||
So in this table, you can define that paper documents classified as Restricted should be locked in a cabinet, documents may be transferred within and outside the organization only in a closed envelope, and if sent outside the organization, the document must be mailed with a return receipt service.
As before, ISO 27001 allows you the freedom to set your own rules, and this is usually defined via the Information Classification Policy, or the classification procedures. To read an article about how information classification can be applied in a specific law firm scenario, click here.
So, as you can see, the 4-step classification of documents might be complex, but it does not have to be incomprehensible – ISO 27001 actually allows you great freedom, and you should definitely take advantage of it: make the classification process both adapted to your special needs, but at the same time secure enough so that you can be sure your sensitive information is protected.
If you need help with the information classification process, sign up for a free trial of Conformio, the leading ISO 27001 compliance software.

 Dejan Kosutic
Dejan Kosutic