Updated: March 22, 2023, according to the ISO 27001 2022 revision.
Since more and more data is being processed and stored with third parties, the protection of such data is becoming an increasingly significant issue for information security professionals – it’s no wonder that the new 2022 revision of ISO 27001 has dedicated a set of controls in Annex A to this issue.
But how is it possible to protect the information that is not directly under your control? Here is what ISO 27001 requires when it comes to supplier relationships, supplier information security requirements, and the information security policy.
- Risk assessment
- Screening agreement
- Access control
- Monitoring
- Termination
Supplier relationship and third parties – Why is it not only about suppliers?
In supplier relationships, suppliers are the ones that will handle sensitive information of your company most often. For example, if you outsourced the development of your company software, chances are that the software developer will not only learn about your company processes – they will also have access to your live data, meaning they will probably know what’s most valuable in your company; the same goes if you use cloud services.
But you also may have partners – e.g., you may develop a new product with some other company, and in this process you share with them your most sensitive research & development data in which you invested lots of years and money.
Then there are customers, too. Let’s say you are participating in a tender, and your potential customer asks you to reveal lots of information about your structure, your employees, your strengths and weaknesses, your intellectual property, pricing, etc.; they may even require a visit where they will do an on-site audit. All this basically means they will access your sensitive information, even if you don’t make any deal with them.
The process of supplier relationships and handling third parties
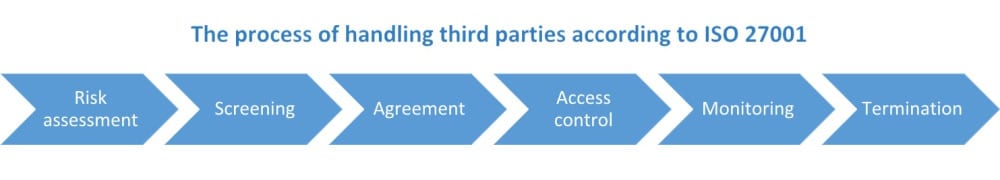
So, how do you protect your information with supplier relationship? Basically, to be compliant with ISO 27001 you should follow this process:
Risk assessment (clause 6.1.2). You should assess the risks to confidentiality, integrity and availability of your information if you outsource part of your processes or allow a third party to access your information. For example, during the risk assessment you may realize that some of your information might be exposed to the public and create huge damage, or that some information may be permanently lost. Based on the results of risk assessment, you can decide whether the next steps in this process are necessary or not – for example, you may not need to perform a background check or insert security clauses for your cafeteria supplier, but you probably will need to do it for your software developer.
Screening (control A.6.1) / auditing. This is where you need to perform background checks on your potential suppliers or partners – the more risks that were identified in the previous step, the more thorough the check needs to be; of course, you always have to make sure you stay within the legal limits when doing this. Available techniques vary widely, and may range from checking the financial information of the company all the way to checking the criminal records of the CEO/owners of the business. You may also need to audit existing supplier information security controls and processes.
Selecting clauses in the agreement (control A.5.20). Once you know which risks exist and what is the specific situation in the company you have chosen as a supplier/partner, you can start drafting the security clauses that need to be inserted in an agreement. There may be dozens of such clauses, ranging from access control and labelling confidential information, all the way to which awareness trainings are needed and which methods of encryption are to be used.
Access control (control A.8.3). Having an agreement with a supplier does not mean they need to access all of your data – you have to make sure you give them the access on a “Need-to-know basis.” That is – they should access only the data that is required for them to perform their job.
Compliance monitoring (control A.5.22). You may hope that your supplier will comply with all the security clauses in the agreement, but this is very often not the case. This is why you have to monitor and, if necessary, audit whether they comply with all the clauses – for instance, if they agreed to give access to your data only to a smaller number of their employees, this is something you need to check.
Termination of the agreement. No matter whether your agreement has ended under friendly or less-than-friendly circumstances, you need to make sure all your assets are returned (control A.5.11), and all access rights are removed (A.5.18).
Focus on what’s important about third-party security
So, if you are purchasing stationery or printer toner, you are probably going to skip most of this process because your risk assessment will allow you to do so; but when hiring a security consultant, or, for that matter, a cleaning service (because they have access to all your facilities in the off hours), you should carefully perform each of the six steps.
As you probably noticed from the above process, it is quite difficult to develop a one-size-fits-all checklist for checking the security of a supplier – rather, you should use this process to figure out for yourself what is the most appropriate approach to protect your most valuable information.
To see how to handle suppliers securely using a compliance tool, sign up for a free trial of Conformio, the leading ISO 27001 compliance software.

 Dejan Kosutic
Dejan Kosutic