Last updated on March 10, 2022.
Contrary to the popular belief that ISO 31000 is now mandatory for ISO 27001 implementation, this is not true. However, when comparing ISO 27001 vs. ISO 31000, the latter could be quite useful for ISO 27001 implementation – it not only offers a couple of good guidelines, but it also gives a strategic context for managing (information security) risks.
But let’s go through the basics first…
In clause 4.1, ISO 27001 notes that you could consider the external and internal contexts of the organization according to clause 5.3 of ISO 31000. In clause 6.1.3, ISO 27001 notes that information security management in ISO 27001 is aligned with ISO 31000.
What is ISO 31000?
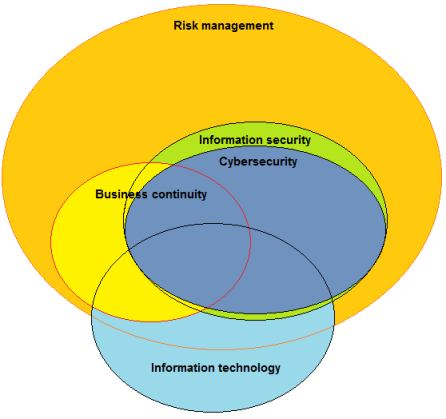
ISO 31000 provides guidelines on how to organize risk management in organizations – the standard is not focused solely on information security risks; it can be used for any type of risks including business continuity, market, currency, credit, operational, and others.
It provides a detailed glossary of risk management terms, explains basic principles of risk management, and provides a general framework including a PDCA cycle (planning, implementing, monitoring and improving – Plan/Do/Check/Act) for risk management. However, being applicable to any type of organization and to any type of risk, it does not provide specific methodology for, e.g., information security risk management.
Relationship between ISO 31000 and ISO 27001
When analyzing ISO 27001 vs. ISO 31000, we may notice that the previous revision of ISO 27001 (from 2005) did not mention ISO 31000, but the new 2013 revision does, and this is what has caused confusion – many people think they have to implement something new in ISO 27001 because of ISO 31000, but this is not true.
Let’s see what exactly ISO 27001 says about ISO 31000:
In clause 4.1, ISO 27001 notes that you could consider the external and internal contexts of the organization according to clause 5.3 of ISO 31000. And, indeed, clauses 5.3.2 and 5.3.3 of ISO 31000 are quite useful in that respect because they provide valuable guidelines on internal and external contexts; however, ISO 27001 mentions ISO 31000 only in a note, which means these guidelines are not mandatory.
In clause 6.1.3, ISO 27001 notes that information security management in ISO 27001 is aligned with ISO 31000. Therefore, ISO 27001 does not say you need to implement risk assessment and treatment according to ISO 31000 – it only says that all the requirements from ISO 27001 are already compliant with ISO 31000. Therefore, you can implement risk management in any way you wish, as long as it is compliant with ISO 27001. (Check also this webinar: The basics of risk assessment and treatment according to ISO 27001.)
And this is it – there is nothing else to it.
ISO 31000 vs. ISO 27005
As mentioned in the previous section that describes ISO 27001 vs. ISO 31000 comparison, ISO 31000 does not offer any specific advice about information security risk assessment and risk treatment; for that purpose, ISO 27005 – a standard that gives guidelines for information security risk assessment and treatment – is much better. It gives you the know-how to identify assets, threats and vulnerabilities, to assess consequences and probability, to calculate risk, etc. And, it is completely compliant with ISO 31000.
So, why would you use ISO 31000? Besides those already mentioned guidelines for identifying internal and external contexts, its biggest value is in providing a framework for managing all kinds of risks on a company-wide level – it can help you turn risk management from some obscure, hard-to-understand issue into a mindset that is easily understood by everyone in the company.
Since ISO 31000 describes how to approach risk management strategically and comprehensively, you can consider this standard to be an excellent framework for Enterprise Risk Management (ERM). So, once you master your information security risk management, you can use it as a foundation for building the ERM.
To see how to use the ISO 27001 Risk Register with catalogs of assets, threats, and vulnerabilities, and get automated suggestions on how they are related, sign up for a free trial of Conformio, the leading ISO 27001 compliance software.

 Dejan Kosutic
Dejan Kosutic