In the beginning of ISO 27001 or ISO 22301 implementation, records might seem like one of those bureaucratic requirements of these standards with no real purpose, and that will only take up your time. However, chances are you already have many records that can be used, and the ones you’ll have to introduce could be quite helpful.
What are records
ISO/IEC 27000:2014 defines records as “evidence of the results achieved” – this basically means that records are produced (automatically or manually) when a certain activity is performed, and those records show what has been done. For example, if your backup is performed automatically, your back-up system will produce logs (which are also a type of records); if you have a visitor’s book, logging names into this book is a record.
All the ISO management standards like ISO 9001, ISO 14001, ISO 20000, etc. have the same requirements for managing records– therefore, this article is applicable to all these standards.
To makes things a bit more complicated, the new ISO 27001:2013 and ISO 22301:2012 standards speak about records only in the context of documented information – documented information is nothing else but records and documents (i.e., policies, procedures, plans, and other similar documents) merged into a single term. This has been done because management of documents and records is basically the same, and in some cases the documents are also the records at the same time.
Examples of records
Below are a couple of records divided by the way they are created:
Automatically created records:
- logs created within information systems
- reports created from the information systems
Manually created records:
- reports where additional input was needed
- training records
- records from drills, testing, and exercising
- meeting minutes
- corrective actions
- asset inventories
- checklists
- to-do lists
- change history within documents
- post-incident review results
- visitors log book
Of course, records can be in paper, digital, or some other form – some records are still predominantly in paper form (e.g., a signed NDA), but the general trend is, of course, to have digital records.
Here you’ll find a list of all mandatory records according to these two standards: List of mandatory documents required by ISO 27001 and Mandatory documents required by ISO 22301 – this is the minimum you need to maintain if you want to comply with these two standards, and other records are necessary if you want to prove you performed certain activities.
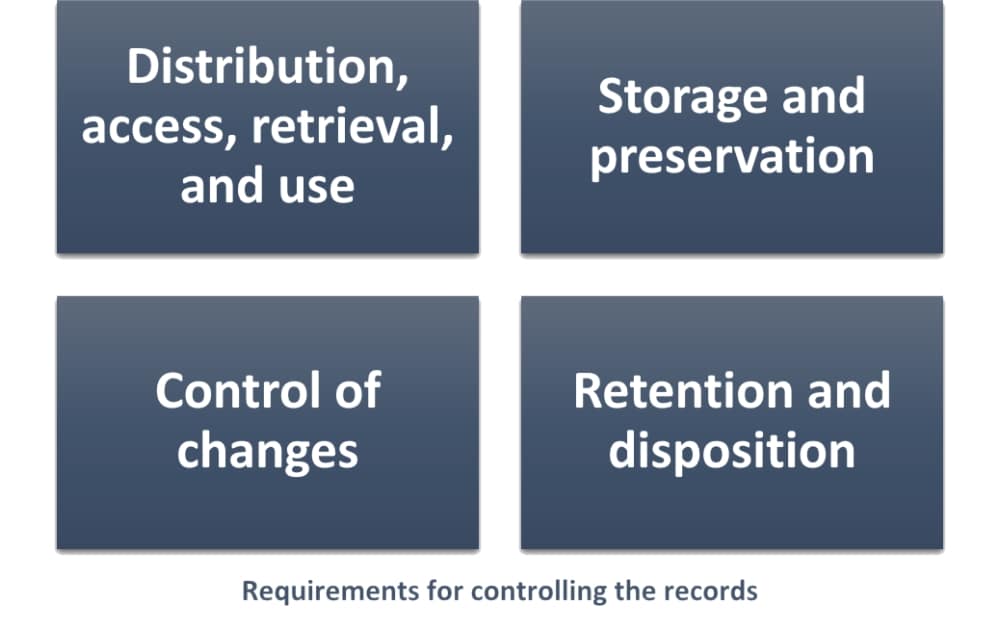
Requirements for controlling the records
Requirements for records management (management of documented information) are almost the same in ISO 27001 and ISO 22301 – here is what these two standards require for the control of records:
- Distribution, access, retrieval, and use – basically, you need to define who has the right to access the records (e.g., by job title) and for what purpose (e.g., read-only).
- Storage and preservation – where the records will be archived (e.g., which computer, which facility), how they will be protected from unauthorized access (e.g., access control, encryption, etc.), and how to preserve their legibility (how to ensure the information is readable even if media became obsolete – e.g., what to do with old VHS video tapes).
- Control of changes – if you edit a particular record (e.g., a report), you need to assign a new version number each time.
- Retention and disposition – how long will a particular record be kept (e.g., 5 years) and how will you destroy such a record (e.g., overwriting digital records, or destroying paper documents in a shredder).
There are basically two ways to document these rules: (a) to write a centralized policy or a procedure that would define rules for controlling all the records in a company, or (b) to define the rules in different policies and procedures separately for each type of record. For example, approach (b) could be a Backup procedure that would define rules for all the 4 above-mentioned bullets specifically for backup logs.
Personally, I think that approach (a) is possible only if there are very few types of records in a company – e.g., if it is a very small company, or if all the company records are very similar; approach (b) should be used in all other cases.
Why are the records important?
As you might have guessed, records are extremely important for the certification audit – the certification auditor will be looking for evidence that you have performed certain activities, and based on that he will make a decision regarding whether you have complied with your documentation. See also: Becoming ISO 27001 certified – How to prepare for certification audit.
But, most importantly – without records you wouldn’t know what you have done and what you haven’t, what’s going well and what isn’t. Would you be able to remember what you agreed on during each meeting in the last couple of years? Would you be able to know whether you performed all the items from your to-do list, and which ones you left for later? Would you be able to know which of your systems performed well and which did not?
Of course you wouldn’t – therefore, use those records to manage your information security, and to manage your company. Without records you’re just guessing – it would be like driving a car in the middle of the night with the lights off.
To implement ISO 27001 & ISO 22301 easily and efficiently, use our ISO 27001 & ISO 22301 Premium Documentation Toolkit that provides step-by-step guidance and all documents for full ISO 27001 & ISO 22301 compliance.

 Dejan Kosutic
Dejan Kosutic