Filters
Standard
Type
Topic
clear search
Filters
clear filters
Standard
Type
Topic
Articles
ISO 27001
The biggest shortcomings of ISO 27001
by Dejan Kosutic
Articles
ISO 27001
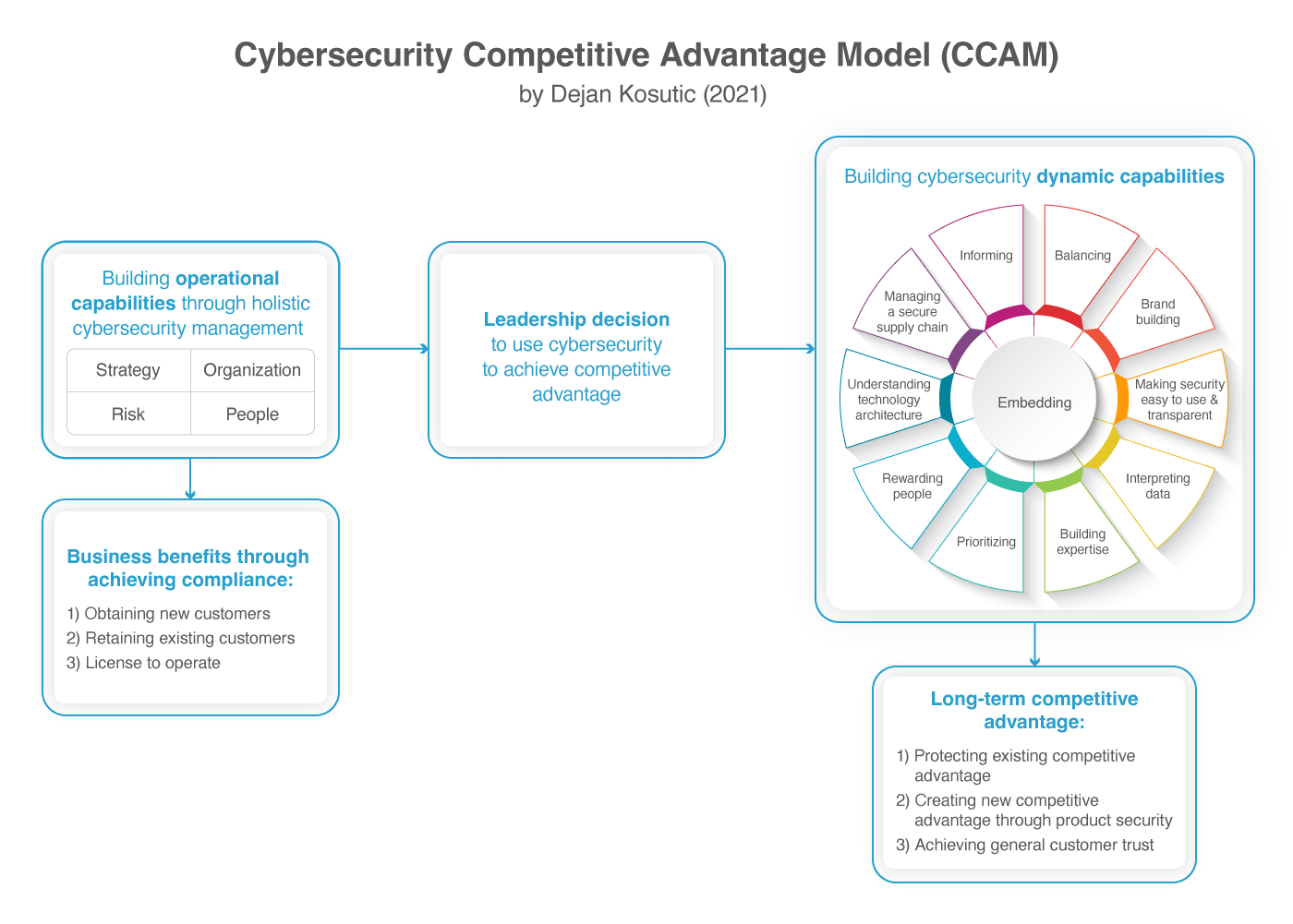
How to achieve sustainable competitive advantage through cybersecurity
by Dejan Kosutic

Articles
ISO 27001
Understanding ISO 27001 Language
by Rhand Leal

Articles
ISO 27001
4 crucial techniques for convincing your top management about ISO 27001 implementation
by Dejan Kosutic
Articles
ISO 27001
5 greatest myths about ISO 27001
by Dejan Kosutic

Articles
ISO 27001
Main changes in the new ISO 27002
by Dejan Kosutic
Articles
ISO 27001
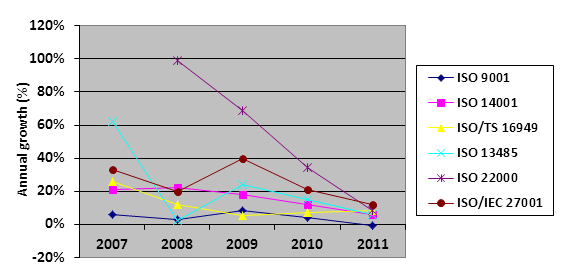
Is ISO 27001 among the top ISO standards?
by Dejan Kosutic

Articles
ISO 27001
Lessons learned from ISO 27001 implementation
by Dejan Kosutic
Articles
ISO 27001
Is it possible to calculate the Return on Security Investment (ROSI)?
by Dejan Kosutic

Articles
ISO 27001
Should information security focus on asset protection, compliance, or corporate governance?
by Dejan Kosutic

Articles
ISO 27001
Information security or IT security?
by Dejan Kosutic
Articles
ISO 27001
5 ways to avoid overhead with ISO 27001 (and keep the costs down)
by Dejan Kosutic
Articles
ISO 27001
How to make a transition from ISO 27001 2005 revision to 2013 revision
by Dejan Kosutic

Articles
ISO 27001
Cloud computing and ISO 27001 / BS 25999
by Dejan Kosutic
Articles
ISO 27001
4 reasons why ISO 27001 is useful for techies
by Dejan Kosutic

Articles
ISO 27001
The most popular ISO 27001 & ISO 22301 blog posts
by Dejan Kosutic

Articles
ISO 27001
What is cybersecurity and how can ISO 27001 help?
by Dejan Kosutic

Articles
ISO 27001
What Can War Teach Us About Mainframe Security?
by Vaune M. Carr

Articles
ISO 27001
List of free ISO 27001 and ISO 22301 resources
by Dejan Kosutic

Articles
ISO 27001
Lessons learned from WikiLeaks: What is exactly information security?
by Dejan Kosutic

Articles
ISO 27001
A first look at the new ISO 27001
by Dejan Kosutic

Articles
ISO 27001
Small business guide to cyber security: 6 steps against the data breach
by Dejan Kosutic
Articles
ISO 27001
Will a piece of paper stop the attackers?
by Dejan Kosutic
Articles
ISO 27001
Implement ISO 27001 according to current 2005 revision, or wait for new 2013 revision?
by Dejan Kosutic
Articles
ISO 27001
Top 10 information security blogs
by Dejan Kosutic

Articles
ISO 27001
Management’s view of information security
by Dejan Kosutic

Articles
ISO 27001
Top 10 information security bloggers in 2014
by Dejan Kosutic
Articles
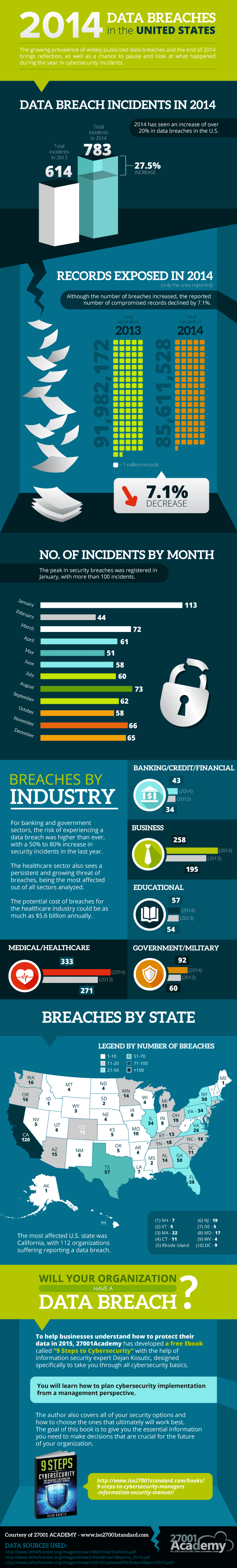
ISO 27001
2014 Data Breaches in the United States
by Dejan Kosutic

Articles
ISO 27001
Cybersecurity Executive Order confirms how crucial information security is for critical infrastructure
by Dejan Kosutic
Articles
ISO 27001
What is ISO 27001? Quick and easy explanation.
by Dejan Kosutic
Articles
ISO 27001
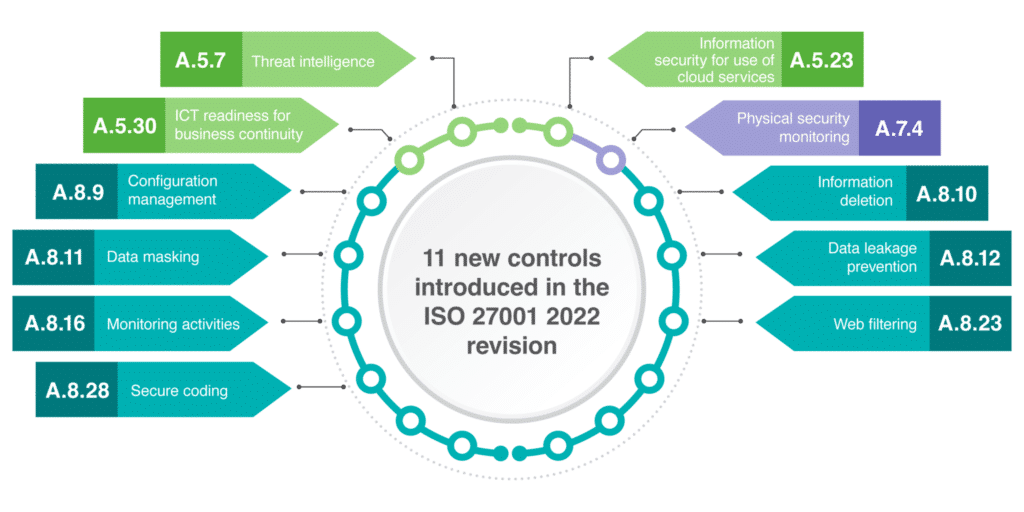
Detailed explanation of 11 new security controls in ISO 27001:2022
by Dejan Kosutic

Articles
ISO 27001
Laws and regulations on information security and business continuity by country
by Dejan Kosutic
Articles
ISO 27001
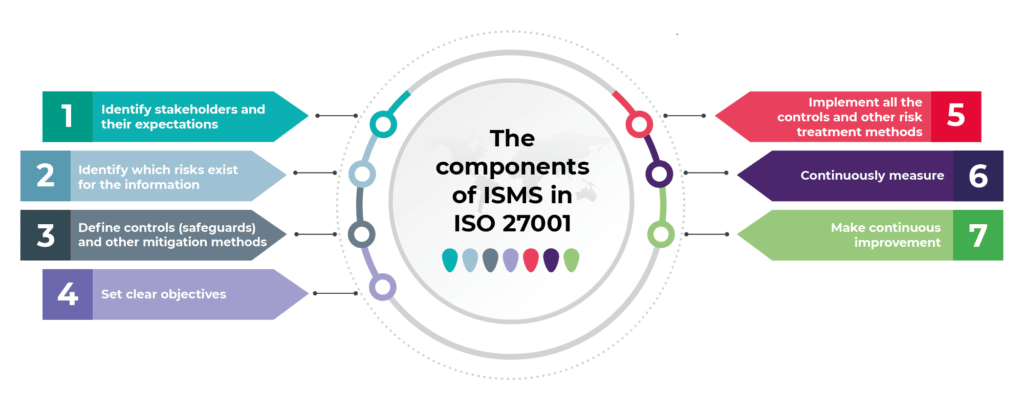
What is an Information Security Management System (ISMS) according to ISO 27001?
by Dejan Kosutic
Articles
ISO 27001
The basic logic of ISO 27001: How does information security work?
by Dejan Kosutic

Articles
ISO 27001
Where to start from with ISO 27001
by Dejan Kosutic
Sort by:
We couldn't find anything
Try adjusting filters or let us help you quickly find what you need by answering a few questions.