ISO 27001 – Where to Start?
Recommended by
 Dejan Kosutic
Dejan Kosutic
 Dejan Kosutic
Dejan Kosutic
Best Articles to Start With
Articles
ISO 27001
What is ISO 27001? Quick and Easy Explanation.
by Dejan Kosutic
Best Tools to Implement and Learn
Conformio ISO 27001 software
Simplifies ISO 27001 certification effort by guiding you through implementation steps and creating documentation automatically.
ISO 27001 Documentation Toolkits
All of the key ISO 27001 documents, records, and templates necessary to complete your certification process.
ISO 27001 Trainings
World’s most popular ISO 27001 courses for beginners, and for experienced professionals.
Upcoming Webinar
Implementation
view all
AI Tools
AI-Powered
Tools
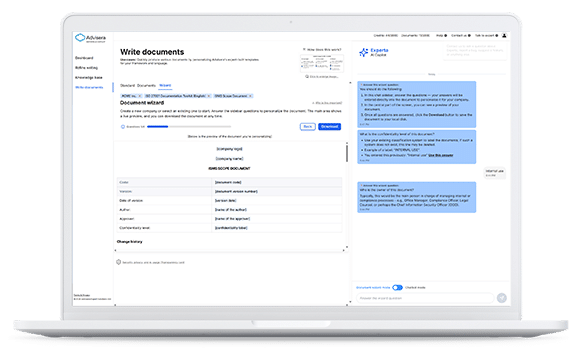
Experta – AI Copilot for ISO 27001 Compliance
The most advanced AI-powered copilot built specifically for compliance work, combining structured expertise with practical implementation tools.
Sign up for free
AI-powered
Regular Toolkits
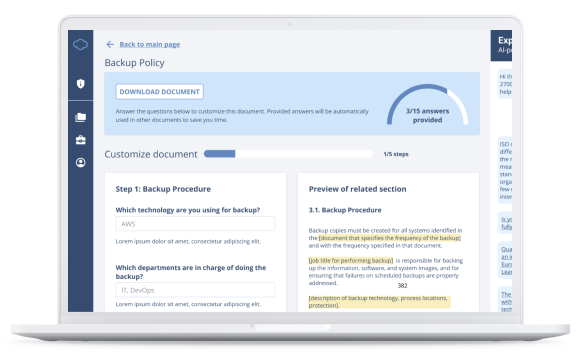
ISO 27001 Documentation Toolkit
Save money and speed up your ISO 27001 implementation process with AI automated document generation software.
Learn more
Documentation
view all
Big Guide to ISO 27001 Clauses

Tools
Discover how ISO 27001 is structured
Easily navigate through ISO 27001 clauses and controls, and for each clause and control, learn what it is, how to document it, how to implement it, and how to prepare for an audit.
Learn More
Certification
Training
view all
ISO 27001 - Where to start?
Learn the basics of starting your ISO 27001 project: how long it will take, how much it will cost, who needs to participate in the project, and how much effort is needed. This video is made for beginners and explains all these preparations in easy-to-understand language.